HEALTHCARE INDUSTRY
Prevention is always better than the cure. Shift your cybersecurity strategy and preempt social engineering attacks that circumvent your security controls.
Picnic reduces individual risk. corporate risk. threat exposure. the human attack surface. the number of incidents. cybersecurity workload. cybersecurity operational costs. |
Most threat actors in the Healthcare sector target executives, employees, and contractors with privileged technical access to operational technology and the Internet of Medical Things (IoMT). Front desk employees with privileged access to patient information are also being targeted. The attackers’ main motive is financial, and their main goal is to deploy and detonate ransomware payloads and steal patient information, which they can sell on the dark web. They rely on spear phishing and exploit infrastructure and supply chain vulnerabilities (human and technical) to execute their attack plan. But first, they conduct target reconnaissance to identify opportunities to attack and build dossiers of their intended victims by leveraging open source intelligence sources (OSINT) in the open, deep, and dark web, looking at professional and personal digital identities.
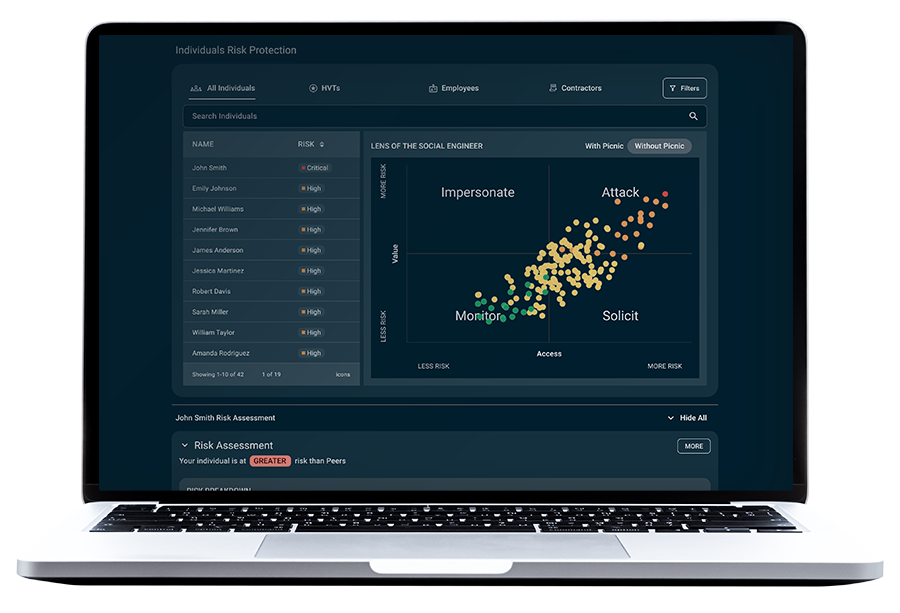
Picnic taps into the same OSINT sources cyber criminals use, and it operates its proprietary technology to:
- Analyze human risk
- Predict attack pathways
- Deliver prioritized remediations that harden your human attack surface to prevent social engineering attacks that impact healthcare services
By partnering with Picnic to make your organizations a tough target for attackers, you will see a quantifiable reduction in impersonation, spear phishing, and credential stuffing attacks, closing the door to data theft, ransomware, and extortion before they can happen.
Picnic delivers security outcomes


Why reduce human risk, and why now?
Ninety percent of all cyberattacks start with a phishing email.
The number of patient records impacted by cyberattacks grew by more than sixty percent in just half a year.
The number of reported data breaches in the Healthcare sector grew by over one hundred percent in a year.
The number of cyberattacks on the Healthcare supply chain grew by over two hundred seventy percent.
Stop reacting. Start preempting.
Cybercriminals circumvent your traditional security controls by exploiting human vulnerabilities before they can exploit technical ones.
Explore our services
Most customers start protecting their human attack surface with Picnic High-Value Target DRPS and then expand coverage.
However, every organization has different priorities and goals. Tell us yours, and we will tailor a program that meets your needs.
Ready to get started?
Move beyond the corporate perimeter to reduce human risk and proactively safeguard against cyber threats with zero effort.
Resources
- All Posts
- Blog
- Customer Success Stories
- In the News
- On-Demand Webinars
- Podcasts
- Press Releases
- Target Intelligence
- Threat Intelligence
- Videos
- Whitepapers

If you want to learn about Picnic and how we protect the human attack surface with digital risk protection services, this is the webinar to watch. Matt Polak, CEO and founder

Howard Miller is the CIO at UCLA Anderson School of Management. He has been a Picnic customer for a few months and, in this video, shares the challenges Picnic helps

Download PDF Incident Name: Henry Ford Health Data Breach Date of Public Report: July 18th, 2023 Date of Incident: March 3rd, 2023 Summary: Henry Ford Health is a Detroit based